-
chevron_right
What We Do in the /etc/shadow – Cryptography with Passwords
pubsub.slavino.sk / dholecrypto · Thursday, 29 December, 2022 - 15:44 edit
Značky: #Cryptography, #Network, #OPAQUE, #PBKDF2
What We Do in the /etc/shadow – Cryptography with Passwords
pubsub.slavino.sk / dholecrypto · Thursday, 29 December, 2022 - 15:44 edit
Značky: #Cryptography, #Network, #OPAQUE, #PBKDF2
Extending the AES-GCM Nonce Without Nightmare Fuel
pubsub.slavino.sk / dholecrypto · Wednesday, 21 December, 2022 - 19:11 edit
Značky: #cryptography, #AES-GCM, #XChaCha20, #Network, #Cryptography
 chevron_right
chevron_right
It took nearly 500 years for researchers to crack Charles V’s secret code
news.movim.eu / ArsTechnica · Tuesday, 29 November, 2022 - 20:48 · 1 minute
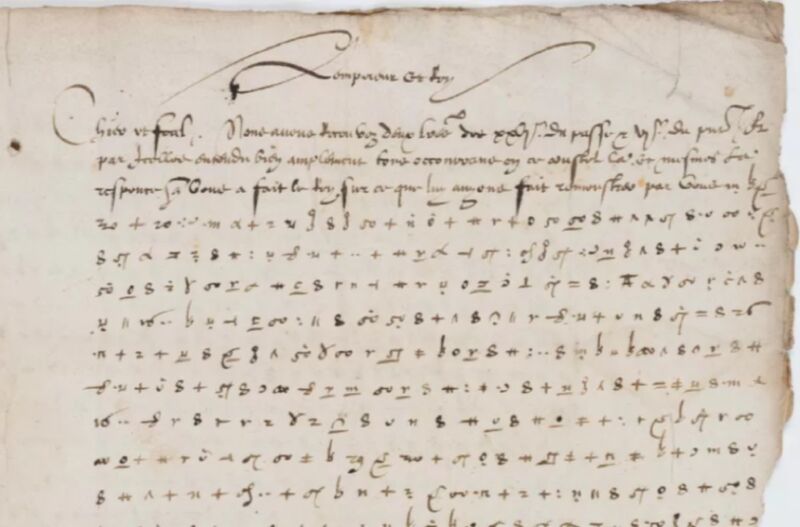
Enlarge / Researchers have finally cracked the secret code of this 1547 letter from Holy Roman Emperor Charles V to his ambassador. (credit: Bibliotheque Stanislas de Nancy)
In 1547, Holy Roman Emperor Charles V penned a letter to his ambassador, Jean de Saint-Mauris, part of which was written in the ruler's secret code. Nearly five centuries later, researchers have finally cracked that code , revealing Charles V's fear of a secret assassination plot and continued tensions with France, despite having signed a peace treaty with the French king a few years earlier.
The future Holy Roman Emperor was born in 1500 to Philip of Hapsburg and Joanna of Trastamara—daughter of Ferdinand II of Aragon and Isabella I of Castile in Spain. She was nicknamed "Joanna the Mad" because of her rumored mental illness and actually gave birth to Charles in a bathroom in the wee hours because she insisted on attending a ball despite clearly having labor pains. Generations of inbreeding conferred on Charles an enlarged jaw (mandibular prognathism), a condition that later became known as "Hapsburg jaw," since it became even worse in subsequent generations. Charles also suffered from epilepsy and gout; the latter became so severe late in life that he had to be carried around in a sedan chair.
Charles V began inheriting various family titles at a young age, and his dominion eventually encompassed the Holy Roman Empire—which extended from Germany to northern Italy in the early 16th century and included Austrian hereditary lands, the Burgundian states, and the Kingdom of Spain. During his reign, he continued the Spanish colonization of the Americas and embarked on a short-lived German colonization effort, earning the label "the empire on which the sun never sets." As his health deteriorated, Charles V abdicated as emperor in favor of his brother Ferdinand in 1556, although it was not legally recognized until February 1558. He retired to the Monastery of Yuste in 1557 and died the following September.
Towards End-to-End Encryption for Direct Messages in the Fediverse
pubsub.slavino.sk / dholecrypto · Tuesday, 22 November, 2022 - 10:57 edit
Značky: #Network, #Twitter, #Cryptography
Cryptographic Agility and Superior Alternatives
pubsub.slavino.sk / dholecrypto · Saturday, 20 August, 2022 - 21:50 edit
Značky: #Network, #JWT, #Vulnerability, #cryptography, #Cryptography
Burning Trust at the Quantum Village at DEFCON 30
pubsub.slavino.sk / dholecrypto · Thursday, 18 August, 2022 - 05:05 edit
Značky: #Network, #JWT, #cryptography, #QKD, #Cryptography, #DEFCON, #Bullshit, #QuintessenceLabs
 chevron_right
chevron_right
Scientists hid encryption key for Wizard of Oz text in plastic molecules
news.movim.eu / ArsTechnica · Monday, 8 August, 2022 - 21:46 · 1 minute
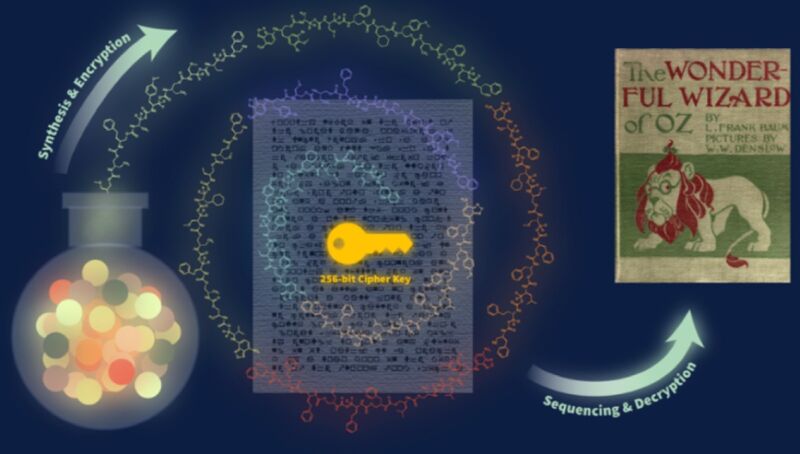
Enlarge / Scientists from the University of Texas at Austin encrypted the key to decode text of the The Wizard of Oz in polymers. (credit: S.D. Dahlhauser et al., 2022)
Scientists from the University of Texas at Austin sent a letter to colleagues in Massachusetts with a secret message: an encryption key to unlock a text file of L. Frank Baum's classic novel The Wonderful Wizard of Oz . The twist: The encryption key was hidden in a special ink laced with polymers, They described their work in a recent paper published in the journal ACS Central Science.
When it comes to alternative means for data storage and retrieval, the goal is to store data in the smallest amount of space in a durable and readable format. Among polymers, DNA has long been the front runner in that regard. As we've reported previously , DNA has four chemical building blocks—adenine (A), thymine (T), guanine (G), and cytosine (C)—which constitute a type of code. Information can be stored in DNA by converting the data from binary code to a base-4 code and assigning it one of the four letters. A single gram of DNA can represent nearly 1 billion terabytes (1 zettabyte) of data. And the stored data can be preserved for long periods—decades, or even centuries.
There have been some inventive twists on the basic method for DNA storage in recent years. For instance, in 2019, scientists successfully fabricated a 3D-printed version of the Stanford bunny—a common test model in 3D computer graphics—that stored the printing instructions to reproduce the bunny. The bunny holds about 100 kilobytes of data, thanks to the addition of DNA-containing nanobeads to the plastic used to 3D print it. And scientists at the University of Washington recently recorded K-Pop lyrics directly onto living cells using a "DNA typewriter."
Guidance for Choosing an Elliptic Curve Signature Algorithm in 2022
pubsub.slavino.sk / dholecrypto · Thursday, 19 May, 2022 - 07:36 edit
Značky: #Network, #secp256r1, #secp521r1, #P-256, #cryptography, #secp256k1, #Cryptography, #secp384r1, #P-384, #ECDSA, #P-521, #Ed25519, #Ed448, #EdDSA
Using RSA Securely in 2022
pubsub.slavino.sk / dholecrypto · Thursday, 10 February, 2022 - 00:11 edit
Značky: #Network, #cryptography, #RSA, #Cryptography