What Is Tor?
The Onion Router or Tor is a network that enables a user to stay anonymous on the internet and get rid of any possible surveillance, user identification, or location tracking while using the internet. You can access the Tor network with the help of a modified Mozilla Firefox ESR web browser.
Tor allows a person to browse the web anonymously by veiling the actual identity of the user. It protects the user from any traffic analysis and network spying.
Tor is perhaps the most popular and secure option available for anonymous internet connectivity. To reduce the confusion, here we are talking about the Tor network, not the Tor web browser, which is used to access the same.
Who Created Tor?
Tor uses the principle of ‘Onion Routing,’ which was developed by Paul Syverson, Michael G. Reed, and David Goldschlag at the United States Naval Research Laboratory in 1990s. Further development was carried out under the financial roof of the Electronic Frontier Foundation (EFF).
Tor Project Inc. is a non-profit organization that currently maintains Tor and is responsible for its development. It has received funds from the US government primarily, and additional aid from the Swedish Government and different NGOs & individual sponsors.
How Does Tor Work?
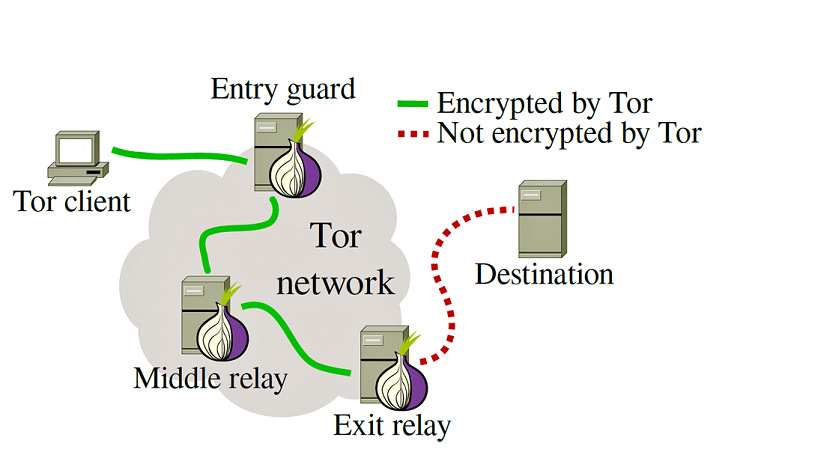
Tor uses the concept of the ‘Onion Routing’ method in which the user data is first encrypted and then transferred through different relays present in the Tor network. Thus, it creates multi-layered encryption (layers like an onion) and a hard-to-follow path to keep the identity of the user safe. As a result, nobody can link your identity to any single point.
One encryption layer is decrypted at each successive Tor relay, and the remaining data is forwarded to any random relay until it reaches its destination server. For the destination server, the last Tor node/exit relay appears as the origin of the data. It is thus tough to trace the identity of the user or the server by any surveillance system acting as the middleman.
Other than providing anonymity to standalone users, Tor can also provide anonymity to websites and servers in the form of Tor Hidden Services. Also, P2P applications like BitTorrent can be configured to use the Tor network and download torrent files.
Also Read:
How To Share Files Anonymously Using Tor’s Darknet And OnionShare?
Is using Tor illegal?
No. Tor browser and dark web aren’t illegal on their own. However, if you end up performing some illegal activity on the dark web using Tor, that’ll surely invite trouble. So, as always, we recommend that you use this technology to perform legal actions and enhance your privacy.
Tor And NSA Connection
The NSA whistle-blower Edward Snowden used Tor to leak information about PRISM to The Guardian and The Washington Post.
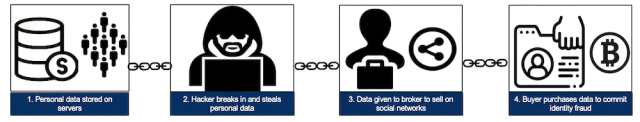
However, the story is not all good-good. Tor faces criticism for the reason that it acts as a medium for different illegal activities like data breaching, drug dealing, gambling, being home to dark web sites. Tor is also used by criminal minds to communicate over the internet while keeping their identity hidden, which makes it difficult for the security agencies to trace them.
The U.S. National Security Agency (NSA) has called Tor “the King of high secure, low latency Internet anonymity.” And it has received similar comments by BusinessWeek magazine, “perhaps the most effective means of defeating the online surveillance efforts of intelligence agencies around the world.”
Another speculation made is that Tor takes its funding from the U.S. Government, which may lead to the assumption that NSA may have compromised the identities of individual Tor users. However, Tor’s former executive director Andrew Lewman disclaimed any confederations with NSA.
Is Tor Browser Safe?
Various claims have been made about compromising Tor’s anonymity and security from time to time. The most famous one was the Bad Apple Attack, in which the researchers claimed to have identified around 10k IP addresses of active BitTorrent users who were connected via Tor.
The Heartbleed bug was behind another major compromise in April 2014, which halted the Tor network for several days.
Traffic Fingerprinting
is a method used to analyze web traffic by analyzing the patterns, responses, and packets in a particular direction. This technique can be used to attack the Tor network by making the attacker’s computer act as the guard.
The main vulnerability was found at its exit points, where the level of security is very low as compared to the rest of the Tor network.
Also Read:
TOR Anonymity: Things Not To Do While Using TOR
What is Tor “Browser”?
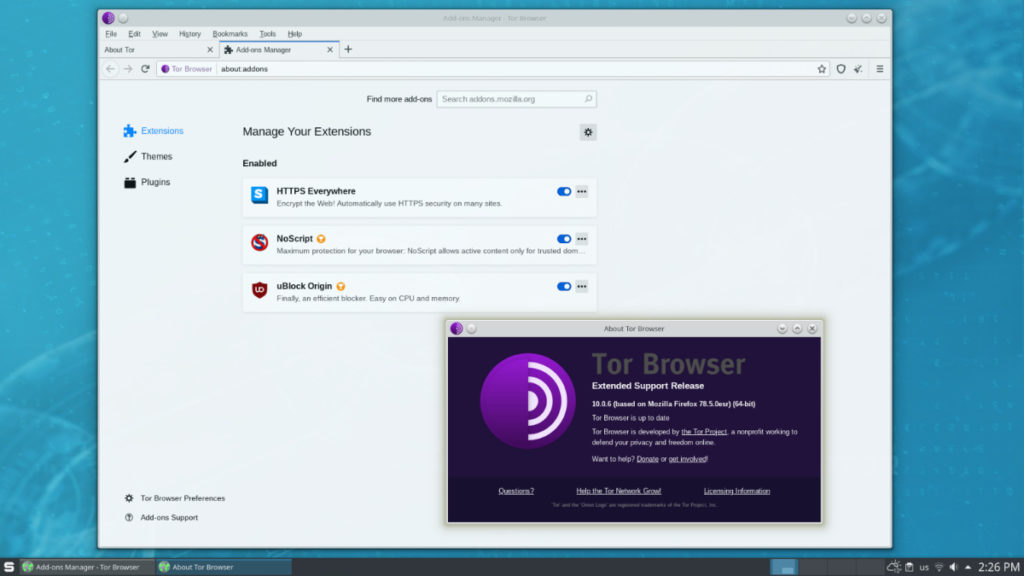
Tor Project Inc. has released
Tor Browser
, which is a modification of an Extended Support Release (ESR) version of the Mozilla Firefox browser. The browser is portable so that it can be used from external media and also reduces the hassel of installation.
Tor Browser removes the browsing history and cookies after every use, thus reducing the risk of any cookie tracking. We can set-up SOCKS (Socket Secure) based applications to use the Tor network by configuring them with a loop-back address.
It’s also known as the dark web browser since it lets users browse the so-called dark web sites that accessible on the regular web.
The Tor browser is available for various desktop operating systems, including Windows, Linux, and macOS. You can visit
this link
to download Tor Browser latest version for Windows, Linux, and macOS.
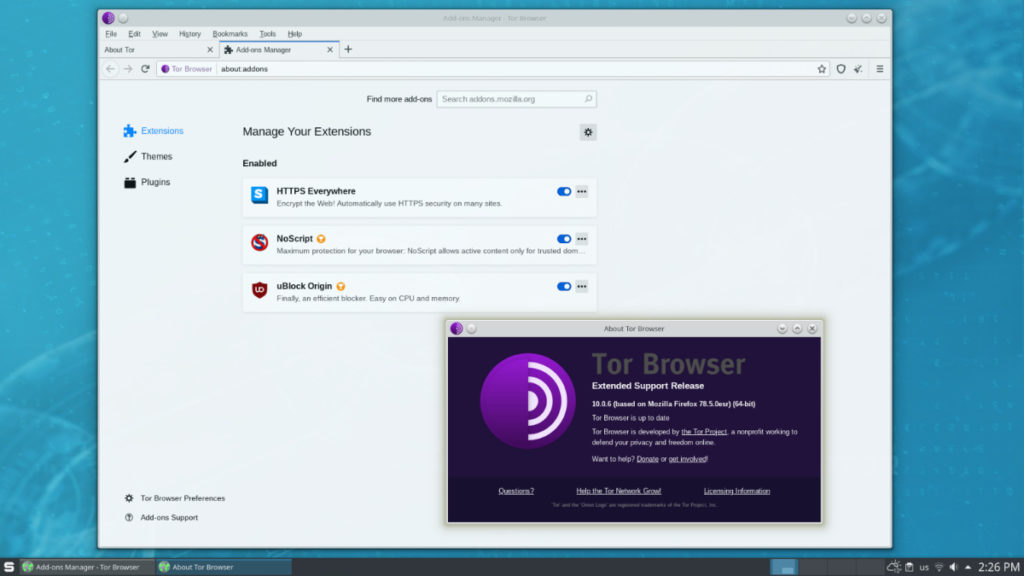
Tor 10.0.6
How to download and use Tor browser?
How to install Tor Browser on Windows 10/7/8?
-
Run the Tor Browser setup.
-
Choose your desired language.
-
On the next window, choose the destination folder. Using Tor would be easy if you choose the Desktop as the destination.
-
Click Install.
The Tor setup will create a folder named Tor Browser on your Desktop. Open the folder, and run the shortcut file to use the Tor Browser.
For Linux, you’ll have to extract the downloaded file, either using the command line or a file extractor application.
Tor Browser for Android
Tor Browser
– official Tor app for Android
Orbot
– a free proxy app with Tor for Android devices.
Orfox – a mobile version of Tor Browser for Android devices. (Discontinued)
The Guardian Project, a global developer community founded by Nathan Freitas, is to be credited for the development of Orfox.
Tor Browser for iOS
A
Tor browser app for iOS
created by Tor Project core contributor Mike Tigas.
Tor Alternatives
I2P and Freenet are other anonymity networks which can act as Tor alternatives. Also, Tails and Subgraph OS are Linux-based distributions with built-in Tor support. In the past, Hornet was also an anonymity network that provided higher network speeds compared to Tor.
To know more about these alternatives, please visit
this link
.
Should I Use Tor?
Tor has proved to be an excellent medium for safe, secure, and anonymous web presence available to a user at no cost. The developers of Tor didn’t intend it to become a hotbed of illegal activities, but evil-minded people have leveraged Tor for their benefits such as selling unlawful stuff on the dark websites. The Tor project has led to an optimistic approach towards censorship and surveillance-free internet.
You can use Tor if you want to conceal your identity on the web or access some websites that blocked in your region. But refrain yourself from doing anything that’s above the law because nothing is fool-proof, and they can still catch you. Also, accessing your social media accounts over Tor can expose your identity.
The post
Tor Explained: What is Tor? How Does It Work? Is It Illegal?
appeared first on
Fossbytes
.
 chevron_right
chevron_right








 Tor 10.0.6
Tor 10.0.6